Are you using ‘test1’ as your password? If so, we’ve got some bad news for you — you’re practically volunteering to become a target for fraudsters. That’s why it’s time to leave ‘password’ and ‘123456’ behind.
Believe it or not, many are struggling to maintain their password hygiene in this dangerous digital age. Unfortunately, recycling your passwords or using your first name as your go-to login information won’t protect you from hackers.
So, the question remains, how to keep away from cybercriminals who are trying to crack your credentials? Keep on reading to find out.
How a Weak Password Can Lead to Data Breaches
At some point, we’ve all been there. Even though you know that the risks are there, you continue to make questionable choices. The same principle applies to credential management. That’s why passwords top the list as one of the hackers’ most valuable information pieces.
As per Verizon’s Data Breach Investigations Report, 61% of breaches occurred because of a weak password. For this reason, it’s no secret that cybercriminals target organizational systems and networks due to the endless opportunities they provide. On top of that, a new survey by GoodFirms showed that 62% of users reset their passwords only when reminded.
Source: securitymagazine.com
Why Your Password Hygiene Should Be a Priority
Have you ever written down a password on a sticky note? Maybe you’ve shared it with a colleague or a friend? Well-known red flags are leading to data theft. The most common bad practices expose users who are applying the same password for multiple platforms. This means they use the same credentials for their banking app and their Tinder account.
Top 5 tips to keep your password secure:
- Never reuse passwords.
- Avoid names or dictionary words.
- Exclude birth year or month/day from your password.
- Avoid sequential numbers or letters (e.g., 1234, qwerty).
- Use at least 12 characters, including numbers or symbols.
As technology advances, you can confidently say that it’s the user’s responsibility to protect their personal details. The more you are prepared, the higher chances are your password will be too challenging to crack.
How to Protect My Password From Cybercriminals?
Many people don’t know how to create a strong password. There’s a chance they don’t have proper password habits. For this reason, you might be one of those people who are now feeling unsafe without a proper password.
We recommend sticking to three key points regarding secure passwords to solve this issue:
- Be cautious. In other words, be aware of suspicious websites that aren’t encrypted. Even if it sounds cliche, believe us when we advise using common sense. Check if the website is legit. If you have doubts before creating an account or entering your password, contact the website owner.
- Don’t recycle your passwords. We’ve mentioned this already, but we’re saying it again. It would be too good to be true to use the same password on all of your accounts.
- Use different characters and symbols. If yours contains multiple uppercase and lowercase letters as well as unique characters — you’re good to go.
Just remember that solid passwords can’t include any personal data. So leave your dog’s name or your birth date out of it. Another great way to solve this issue is to use a random password generator.
Add another layer of security. Book a demo for our fraud prevention solutions! It’s free.
How to Create a Good Password?
You might be wondering, ‘how do I create a good, strong password?’ — the principal’s simple. A strong one is a combination that hackers can’t crack. In other words, both humans and computers should not detect your password. Keep in mind that cybercriminals use special software to go through various letter, number, and symbol combinations.
Their goal is to crack your credentials; therefore, it’s vital to make sure that your password is at least 12 characters long. Another major factor is uppercase and lowercase letters. Also, don’t forget to include special symbols and punctuation.
What is a Strong Password?
According to good old Wikipedia, password strength is measured by the effectiveness against brute-force attacks. Such attacks try to guess every possible combination in the book. That’s why a good password is a mixture of length, complexity, and unpredictability.
Here are the main elements that describe secure credentials:
- The longer the password, the better; the rule you need to live by. Remember, a unique password consists of at least 12 characters.
- Your password should be different for every account you own. Recycling’s great, but not when it comes to passwords.
- Use a mixture of special symbols. If you add various numbers, uppercase and lowercase letters, it’ll be harder to crack your password.
- Think outside the box. Don’t use common substitutions, such as replacing letters with numbers.
- Don’t get too personal. Leave your private information out of your password.
How Do Hackers Steal My Password?
Now that we’ve established the basics let’s switch roles and try to think as scammers do. A password is like a virtual key that opens many doors in the digital world. In other words, a single login can do damage to all of the other networks in your cloud, from your email, and social media accounts, to Uber or Netflix.
At one point, scammers might even steal your personal details to sell them to their fellow criminals. Unfortunately, sometimes it’s not enough to have strong credentials. If you want to avoid the risks of getting hacked, simply learn more about the context behind stolen passwords:
1. Malware
Malicious online adverts, downloads from compromised websites, and phishing are prime examples of sinister malware attacks. Cybercriminals go the extra mile to create legitimate-looking apps and hide malware on third-party application stores to successfully steal your password.
But the wide range of malware doesn’t end here. For instance, keylogging your mouse movements or tracking the strokes typed onto a keyboard allows criminals to quietly collect your info, including credentials. The consequences are severe, starting with data breaches and ending in identity theft.
2. Phishing
Humans aren’t as perfect as we want them to be. When it comes to passwords or cybersecurity, we’re prone to making the wrong decision. One of the most famous examples of human error is phishing.
Bad actors use our weaknesses to pose as legitimate entities or companies that you do business with. The phishing text or email might look authentic, but it includes a malicious link. From this point, if you click on the link and enter your data, it’s game over.
3. Technical Hacks
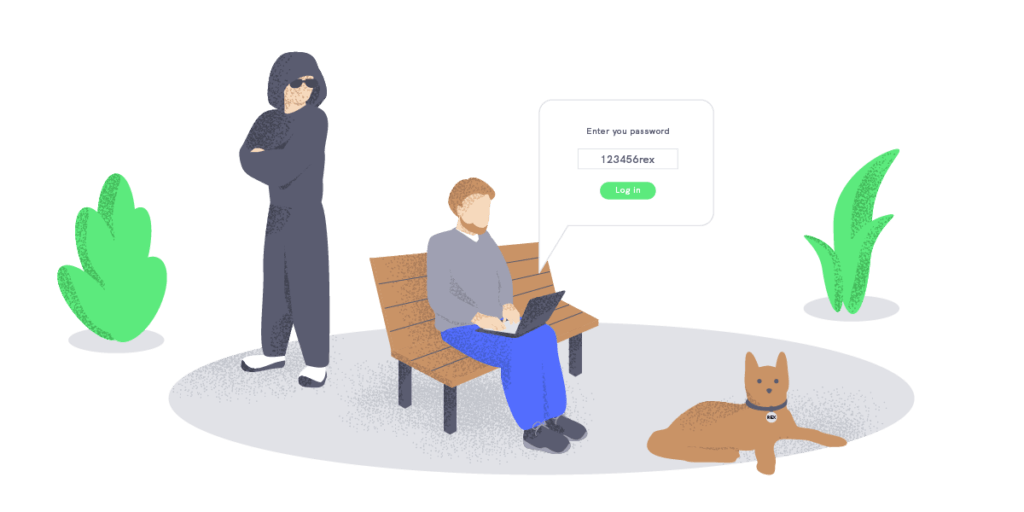
Technology and its inventions have a darker side. Without multi-layer security or good password practices, it’s easier for hackers to steal your data. For instance, special network analyzers monitor data to extract your passwords.
All scammers need to do is gain access to your wireless network. Hackers unlock this key via malware or by physically being there in person. As a solution, experts suggest using VPNs. Since many employees are choosing to work remotely, businesses need to tackle this alarming issue.
What Happens After My Password Gets Stolen?
Some scenarios are more pleasant than others. Bad actors use sensitive data, such as credentials, for malicious purposes. A password is like a golden ticket for more severe crimes. For instance, if cybercriminals steal your digital identity, they can potentially access your healthcare information. Such data is more valuable on the Dark Web than bank account details, going for $158 per stolen record.
In other words, when dangerous doors are opened, hackers gain access to your online identity, putting in danger your personal accounts as well as your business. Regrettably, many organizations don’t take security seriously by knowingly mismanaging passwords and providing the same access rights across employees and third-party vendors.
Protect your password and your business. Discover more here.
Simple Password Methods That’ll Solve Your Issues
You don’t need a strong password if you have nothing to hide. By now, you should be aware that this is one of the most common password myths out there. And yes, special characters and number combinations don’t make your password automatically stronger.
If you’ve set your credentials as ‘PassWord321’ instead of ‘password’, you might want to continue reading.
A handy tip that’ll help you create unhackable credentials is to use the passphrase method. This simple yet effective technique comes with a twist. You need to choose uncommon and strange words and add proper nouns. It can also be a mix of words in other languages.
If you can’t think of anything on the spot, you can construct a passphrase using association. For instance, you can scan your room and add words that you see. In this case, the password could be ‘LampTVComputerBook’. By implementing an image in your head, you’ll remember the password easier.
Another handy tip that’ll help you master your password game is the sentence method. It’s pretty self-explanatory since you need to take a random sentence and turn it into a password. You can try to think of something memorable as well.
For example, let’s say that your sentence is ‘We went to Australia back in summer 2018’. The next step is to take the first two letters of every word. Voilà; you have a new password — ‘WEwetOaubaINsu20’.
Final Thoughts
Having a strong password should be the number one priority in this challenging digital age. Proper credentials serve as the first line of defense against cybercriminals. Once you follow the tips and know all the tricks, you realize that passwords aren’t rocket science.
The stronger the credentials, the more protected your personal data is from hackers’ malicious intents. However, passwords aren’t the only way to protect yourself from cyberattacks. So don’t forget to use multi-layer security at home and for your business.
And if a password is not enough — we’ve got you covered. Let’s talk about stronger security measures, such as identity verification.
This blog post was updated on the 8th of March, 2024, to reflect the latest insights.
Want to know more about efficient cybersecurity measures?
We’d help with security and fraud prevention!