Identity Verification
Useful information and guides about the latest trends in identity verification
June 17, 2024
How Does Student Identity Verification Work?
Explore the options for student identity verification and find out why universities and e-learning apps choose to onboard their learners using third-party KYC software as a way to prevent unwanted fraud scenarios, including forged documents, like fake student visas.

February 23, 2024
Top 5 KYC Challenges and How You Can Overcome Them [In-Depth Explanation]
Learn the key reasons why companies struggle with KYC challenges. Find out how to build a proper identity verification process while keeping up with the regulatory compliance requirements and increasing customer demands — all while exploring real-life use case examples from various industries.

January 29, 2024
What is Reverification? Explanation Guide [Updated]
Find out the key use cases of reverification and learn why this process can be a beneficial factor in both security and user experience.

January 28, 2024
Top 3 KYC Automation Benefits for Businesses
We explore the concept of KYC automation and its use cases, explaining how AI-powered KYC software can improve internal compliance operations for businesses.

December 29, 2023
Video KYC: What Does it Look Like in 2026?
Video KYC goes beyond the traditional hassle of a video call verification process. Previously, customers had to navigate through network, camera, and microphone access checks, along with pre-checks, before engaging in video KYC. However, the contemporary version of the video KYC process is a game-changer. It is now accessible 24/7, not confined to business working hours, while still meeting regulatory requirements and enhancing the overall onboarding experience for customers. Read more.
October 26, 2023
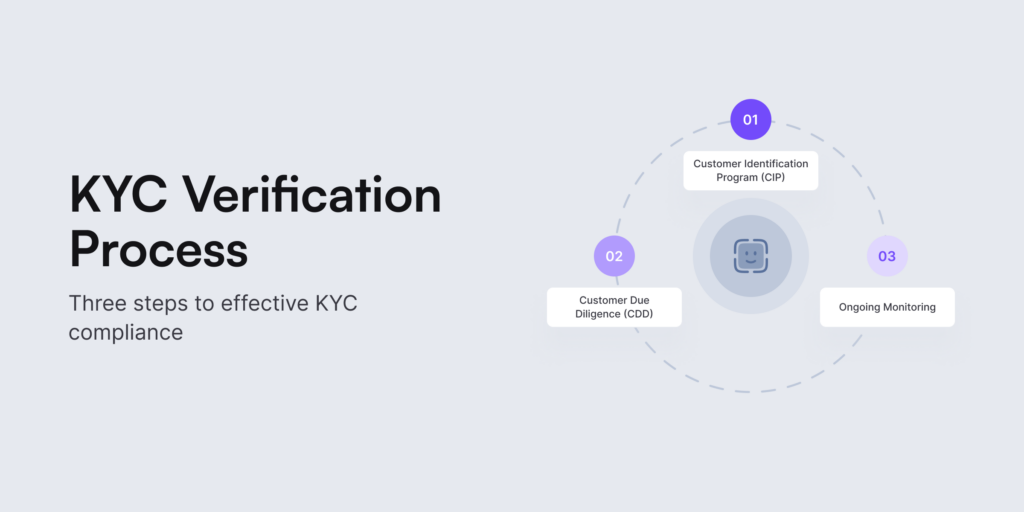
3 Steps to KYC [Compliance Guide]
Knowing your customers properly isn’t possible without KYC or Know Your Customer. Chances are that as soon as you hear this phrase, identity verification comes into mind. Today, this process is also known for strict regulatory compliance across various industries and jurisdictions. What’s the best way to verify a user’s identity? How do we keep the balance between compliance requirements and user experience? What are the 3 steps to KYC? We answer all the burning questions and provide the latest insights below.

October 6, 2023
DEXs and KYC: Addressing Compliance Challenges
Decentralized exchanges (DEXs) are cryptocurrency trading platforms that enable direct transactions between users, aiming to lower transaction fees. They are considered to be fairly anonymous since users need to connect to a crypto wallet to get started. However, DEXs also encounter regulatory hurdles, such as addressing Know Your Customer (KYC) and Anti-Money Laundering (AML) concerns. Read more.

June 9, 2023
How to Choose the Best KYC Compliance Software in 2026?
The size of the KYC compliance software market recently reached USD 9.50 billion. And there’s no surprise here. The rise in identity theft cases is a key driver behind the increasing demand for identity verification solutions. So the real question is – which one’s the best? We prepared a full checklist to help your business choose the right KYC compliance software.

May 10, 2023
Document Verification: How Does the Process Work?
Collection, extraction, validation and verification. These are the vital steps of the document verification process. But what else goes into deciding whether a document, such as a bank statement or an employment record, is actually legitimate or not? We go deeper into this subject, discussing the benefits of online document verification.

February 7, 2023
A Definitive Guide on KYC for Crypto [Updated]
It’s an open secret that cryptocurrencies were introduced to tackle the problems of centralization and lack of authority in finance after the 2008 financial crisis. Though they have been used in illegal activities, they have ended up causing billions of dollars in damage. Read more.

January 26, 2023
Proxy Network Security: Common Use Cases + Identity Verification [Updated]
There’s an ultimate feature that describes all cybercriminals accurately. Spoiler alert – it’s the fact that they want to stay anonymous. For years, proxy servers supported malicious actors, helping them blend in and conduct dangerous crimes. But can identity verification end this era?

January 19, 2023
The Guide to Decentralized Identity in 2023 [Updated 2025]
The internet has been turned into a gold mine for data. Users have filled up their storage banks with millions of data pieces, defining who they are both digitally and IRL. But now Web3 has birthed a new idea by which humans can safely engage with their data through digital identity.

January 5, 2023
Understanding Web3 and its Security Measures
The static, the responsive, and the semantic are seen as how the internet has evolved. The evolution of web3 might be slow with current trends, but positive adoption is being noticed. The ultimate question that still gives headaches to some critics is the security factor. Tag along to find out more.