Identity Verification
Useful information and guides about the latest trends in identity verification
June 13, 2025
How to Check if Someone is Using Your SSN [Tips]
Review the key safety tips and signs that signal SSN misuse that will help protect your identity and your SSN from getting compromised. Learn what SSN fraud is and how SSN verification can help.
April 23, 2025
Best Identity Verification Software Providers of 2025
Choose the right identity verification provider and review the required features for complete KYC compliance.
March 12, 2025
Best KYC Software Providers of 2025
Explore the latest coverage of best KYC software providers and recommendations on where each of the service excels the best.
March 3, 2025
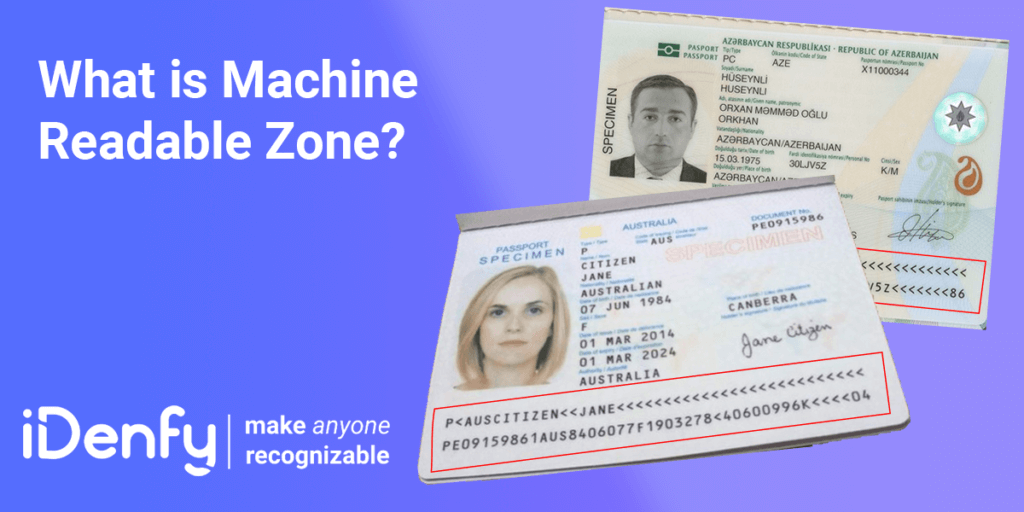
Machine Readable Zone
Wondering what is a machine-readable zone (MRZ)? Do you want to know its role in identity verification? If the answer to these questions is “yes.” Read this blog until the end.

February 28, 2025
KYC Verification [3 Main Components & More]
Access our expert insights regarding KYC verification, with step-by-step examples for different industries, including other AML processes that are mandatory after the initial user onboarding stage.
January 15, 2025
eIDV: Electronic Identity Verification (Definition, Examples & More)
Learn what eIDV is, where and what kind of industries use this electronic identity verification method, which regulatory frameworks require the 2+2 approach, and how it helps with your company’s risk assessment.

September 30, 2024
How to Spot a Fake ID in Different States? [With Examples]
From students using fake IDs to purchase age-restricted items to fraudsters forging ID documents for obtaining loans and other large-scale operations — it’s important to know how to spot a fake ID in different states.
July 24, 2024
Top 5 Identity Verification Measures [For Beginners]
Stricter regulations across new industries, including social media or gaming, and new age verification requirements have pushed businesses beyond the traditional financial sector to find proper identity verification measures that carry multiple features. But is it actually achievable? We review the most popular KYC measures in the market.
June 17, 2024
How Does Student Identity Verification Work?
Explore the options for student identity verification and find out why universities and e-learning apps choose to onboard their learners using third-party KYC software as a way to prevent unwanted fraud scenarios, including forged documents, like fake student visas.
February 23, 2024
Top 5 KYC Challenges and How You Can Overcome Them [In-Depth Explanation]
Learn the key reasons why companies struggle with KYC challenges. Find out how to build a proper identity verification process while keeping up with the regulatory compliance requirements and increasing customer demands — all while exploring real-life use case examples from various industries.

January 29, 2024
What is Reverification? Explanation Guide [2025 Edition]
Find out the key use cases of reverification and learn why this process can be a beneficial factor in both security and user experience.
January 28, 2024
Top 3 KYC Automation Benefits for Businesses
We explore the concept of KYC automation and its use cases, explaining how AI-powered KYC software can improve internal compliance operations for businesses.
October 26, 2023
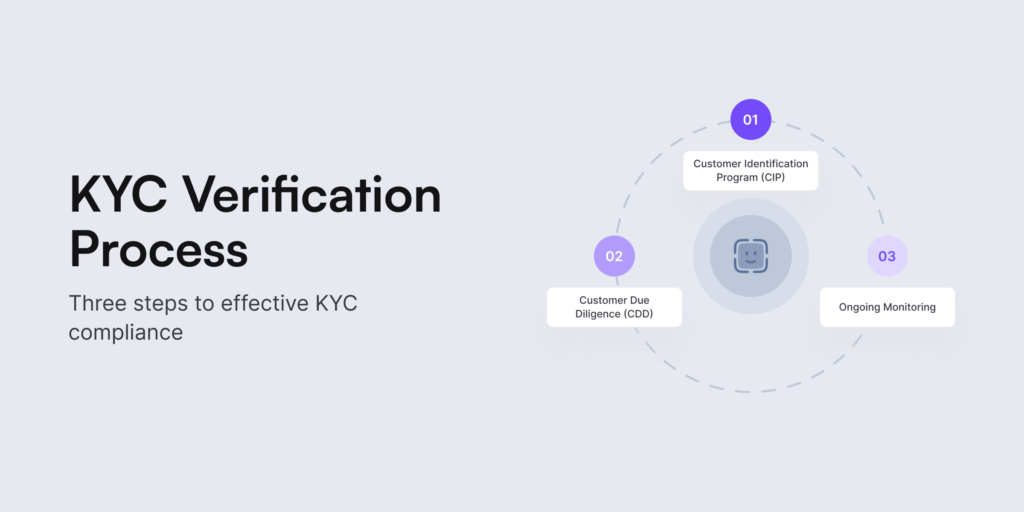
What are the 3 Steps to KYC?
Knowing your customers properly isn’t possible without KYC or Know Your Customer. Chances are that as soon as you hear this phrase, identity verification comes into mind. Today, this process is also known for strict regulatory compliance across various industries and jurisdictions. What’s the best way to verify a user’s identity? How do we keep the balance between compliance requirements and user experience? What are the 3 steps to KYC? We answer all the burning questions and provide the latest insights below.